Planning system and software security
Devices based on the Symbian platform are capable of joining both public and private networks and often have the functionality of a normal desktop computer. However, the average user does not perceive the device as a computer, but rather as a regular phone that is safe from security threats. This creates an opportunity for hostile attackers to infiltrate the device and wreak severe direct or indirect damage (for example, by penetrating into the corporate intranet).
It is, however, possible to anticipate these kinds of threats, and protect applications by using the security features offered by the Symbian platform, and by expanding security policies to cover mobile devices and services.
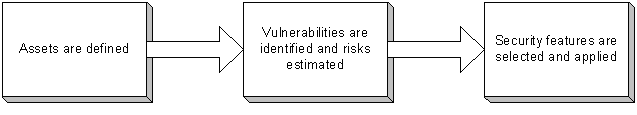
To develop system or software security, repeat the following steps:
Define and evaluate all critical assets (resources, information).
Identify all possible threats, vulnerabilities, and potential attacks, and estimate the extent of possible damage.
Areas to examine in the Symbian platform are system resources, removable media, and communication between components.
Prioritize high-risk vulnerabilities, and select and implement corresponding security features. If risks are sufficiently low, protective measures may be unnecessary.
Repeat these steps until the necessary level of protection is achieved.
The security development process is guided by cost, efficiency, and usability. If security is too tight, this may be expensive and affect both performance and the user's experience of the system or software. On the other hand, if security is too slack, this may result in severe damage and, in the long run, be even more costly.
Security methods
The list below contains the most common and important security methods used in the mobile world:
Ciphering enables confidentiality. Information is accessible only by authorized parties. With ciphering it is also possible to maintain integrity.
Hash function (checksum) can be used to verify integrity and detect information tampering.
Signing allows attaching of information to a certain source.
Authentication ensures that the object is what it claims to be.
Access control restricts unauthorized access to resources.
Authorization is permission to perform tasks on behalf of somebody else.
Certification is provided usually by a third party to prove information validity.
Recovery mechanisms are usually implemented as redundancy (duplication of information or routes).
In communication it is possible to use, for example, error correction to repair transmission failures, random traffic generation to keep the line occupied, and packet uniforming to blend important packets into traffic.
Some of the methods above are interconnected (for example, certification requires that the information is signed) and not all of them are of equal importance, since some basic methods form a base for more complicated methods.
Copyright ©2010 Nokia Corporation and/or its subsidiary(-ies).
All rights
reserved. Unless otherwise stated, these materials are provided under the terms of the Eclipse Public License
v1.0.