Overview of hash algorithms
What is a cryptographic hash?
A cryptographic hash algorithm (also known as a message digest, a one-way function, or simply a hash) takes a variable-length input (the message) and produce a fixed length output known as the hash (or digest) of the input. It is often useful to think of the resulting output as a representation, or fingerprint, of the original input.
There are two properties that are important to cryptographic hashes:
-
it must be hard to find collisions, i.e. it is highly unlikely that two distinct strings will hash to the same output
-
it is extremely difficult to determine the original input given only the output. Even very small changes to the input will give rise to radical changes in the output.
These properties make hash functions useful in cryptography and other applications as they allow the representation of objects in a known fixed size.
The hash algorithms supported by the Symbian platform are:
| Hash algorithms | Further information |
|---|---|
|
MD4 |
|
|
MD5 |
|
|
SHA-1 |
FIPS 180-1 and RFC 3174 |
|
HMAC |
There is also support for MD2 (see RFC 1319 ) and SHA, which is there for backward compatibility, but it is not to be used in new code.
What is an HMAC?
Unlike the hashes mentioned above, HMAC (Hashed Message Authentication Code) is a key-dependant hash. It allows a key to be specified at creation of the HMAC. Only people with that key can verify the hash. HMACs are useful when authentication but not secrecy of a message is required.
The sender appends to the message data an authentication tag (which is a function of the data and the shared key). The recipient recomputes the authentication tag on the received message using the shared key. The integrity of the message is deemed valid only if the two authentication tags match.
For further details see RFC 2104 .
The Hash API
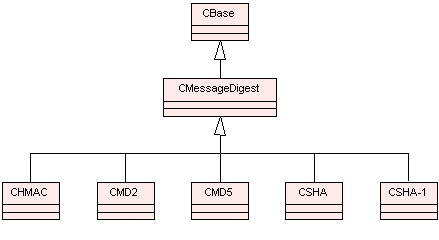
CMessageDigest is the base class for all hash algorithms.
The diagram below show the main classes used in the hash framework. For information on each class see the Cryptography API Reference material.
The hash API is used internally by the Security components: AppInst, Certman (Certificate Management) and Cryptography. Networking/TLS uses a pseudo-random function (PRF) based on HMAC. Both MD5 and SHA-1 are used in TLS.
Copyright ©2010 Nokia Corporation and/or its subsidiary(-ies).
All rights
reserved. Unless otherwise stated, these materials are provided under the terms of the Eclipse Public License
v1.0.